Processors stories

Hands-on review: ASRock Phantom Gaming Z790 Nova WiFi motherboard
Wed, 24th Jan 2024
#
gaming
#
endpoint protection
#
reviews
ASRock's Phantom Gaming Z790 Nova WiFi is one of the new "refresh" LGA 1700 motherboards released in time for the launch of Intel's 14th-gen CPUs, themselves a refresh of last year's Raptor Lake processors. .

Hands-on review: Intel NUC 12-PRO Wall Street Canyon
Tue, 23rd Jan 2024
#
reviews
#
endpoint protection
#
technology gifts
The new Intel NUC impresses with its tiny size and customizable features, offering powerful computing in a compact package.
AI: The focus of Intel and its partners at CES 24 Intel Client Open House
Tue, 16th Jan 2024
#
cloud services
#
endpoint protection
#
edr
Intel, its partners and rivals are all investing in AI technology that will change the way we work, play and get around, likely sooner rather than later.

Intel unveils 14th Gen Core processors at CES
Tue, 9th Jan 2024
#
endpoint protection
#
edr
#
ces
Intel unveils its dynamic 14th Generation Core processor lineup at CES, highlighting the flagship i9-14900HX with 24 cores, boasting top-grade performance for mobile and mainstream systems.

TrustInSoft enhances its software analyser with memory mapping feature
Tue, 12th Dec 2023
#
endpoint protection
#
edr
#
operating systems
TrustInSoft has upgraded its software analyser with a pioneering memory mapping feature, increasing precision in hardware analysis.
Hands-on review: Intel Core i9-14900K and Intel Core i5-14600K 14th -generation CPUs
Tue, 28th Nov 2023
#
pc hardware
#
endpoint protection
#
reviews
Intel has unleashed the company's new 14th-generation desktop processors. We check out the Core i9-14900K flagship CPU and its little sibling, the Core i5-14600K.

Apple introduces the M3, M3 Pro, and M3 Max - most advanced PC chips
Tue, 31st Oct 2023
#
endpoint protection
#
apple
#
technology gifts
Apple unveils new M3 chips with 3-nanometer technology, boosting speed and efficiency in Macs and aiming for carbon neutrality by 2030.
AMD acquires Nod.ai to boost open AI software capabilities
Wed, 11th Oct 2023
#
endpoint protection
#
edr
#
ai
AMD strengthens its AI software competencies with the acquisition of Nod.ai, anticipating enhanced AI solutions for its products.

Getac unveils semi-rugged laptop featuring sustainable design
Thu, 28th Sep 2023
#
sustainable it
#
endpoint protection
#
mobility
The next-generation S410 offers an advanced processor currently available in the rugged industry, with chassis utilising post-consumer recycled materials.

Intel launches suite of AI technologies to shape 'Siliconomy'
Fri, 22nd Sep 2023
#
endpoint protection
#
edr
#
ai
Intel Innovation launches AI technologies to make AI more accessible, with plans to ship millions of new AI-enabled PCs in 2024. #Siliconomy.

Oracle bolsters cloud infrastructure with advanced NVIDIA & Ampere processors
Thu, 21st Sep 2023
#
edr
#
endpoint protection
#
oracle
Oracle's new cloud instances powered by NVIDIA GPUs and Ampere CPUs aim to enhance performance and efficiency for diverse workloads.
Millions of devices & hardware acceleration central to Intel's vision of AI
Wed, 20th Sep 2023
#
pc hardware
#
endpoint protection
#
edr
Intel lays out ambitious vision for AI, aiming to disrupt industries by harnessing the power of computing devices and hardware acceleration.
Intel Reinforces Commitment to Asia Pacific & Japan Region
Fri, 8th Sep 2023
#
endpoint protection
#
it in manufacturing
#
edr
Intel's commitment to innovation and collaboration in the APJ region is highlighted by Steve Long, the VP of Sales and Marketing.
Intel unveils next-gen Xeon with better efficiency architectures
Thu, 31st Aug 2023
#
endpoint protection
#
paas
#
colocation
Intel’s next-gen server platform in 2024 will deliver strong P-core performance for critical workloads, including AI.

Intel unveils Next-Gen Xeon processors with performance and efficiency gains
Tue, 29th Aug 2023
#
endpoint protection
#
edr
#
xeon
Next-gen server platform set to revolutionize performance and efficiency in AI and cloud computing, launching in 2024.

Intel unveils ambitious plans for it's Aurora supercomputing technology
Fri, 25th Aug 2023
#
endpoint protection
#
servers
#
edr
The world's first two exaflop supercomputer is being discussed by Intel, marking a milestone in supercomputing technology.

Intel's EVO standard for Laptops explained
Wed, 23rd Aug 2023
#
endpoint protection
#
mobility
#
tablets & laptops
Intel's EVO standard redefines the laptop experience with superior performance, portability, and display quality, backed by rigorous testing and validation.

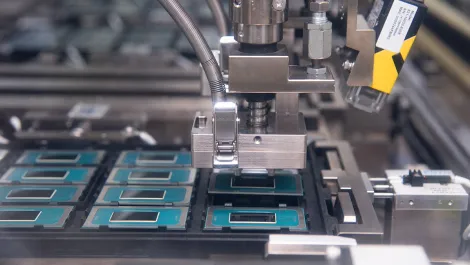
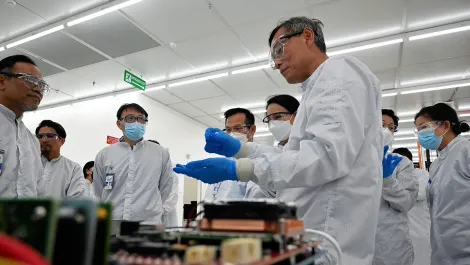
Intel's IDM 2.0: A New Era in Global Manufacturing
Tue, 22nd Aug 2023
#
endpoint protection
#
it in manufacturing
#
edr
Intel unveils IDM 2.0 manufacturing strategy in Malaysia, aiming to remain at the forefront of semiconductors.

Intel and Synopsys expand long-standing partnership
Tue, 15th Aug 2023
#
endpoint protection
#
partner programmes
#
physical security
Intel and Synopsys have expanded their partnership to enable leading IP (intellectual property) on Intel's advanced process Nodes.
Samsung and Intel extend virtualised vRAN collaboration
Thu, 10th Aug 2023
#
virtualisation
#
endpoint protection
#
partner programmes
The new product innovation agreement will deliver cutting-edge vRAN solutions with enhanced performance to meet rising capacity demands.

Intel, Ericsson partner to advance next-gen 5G infrastructure
Fri, 28th Jul 2023
#
endpoint protection
#
partner programmes
#
edr
The announcement signals confidence in 18A process technology and underscores progress on Intel's five-nodes-in-four-year roadmap.
New MLCommons delivers competitive AI gains for Intel
Fri, 30th Jun 2023
#
edr
#
endpoint protection
#
ai
Habana Gaudi2 and 4th Gen Intel Xeon Scalable processors deliver leading performance and optimal cost savings for AI training.

Getac launches latest G-RuggedPro series tablets and laptops
Thu, 13th Apr 2023
#
firewall
#
endpoint protection
#
mobility
Next-generation UX10 and V110 are designed to thrive in challenging field environments, such as those in defence, utilities, and public safety sectors.

New Intel vPro platform provides comprehensive security
Fri, 24th Mar 2023
#
pc hardware
#
endpoint protection
#
edge security
Intel has unveiled the new vPro platform built especially for business, addressing constantly evolving needs with comprehensive security.